R&D at the service of innovation
Our goal: to develop skills and technologies to serve our ecosystem.
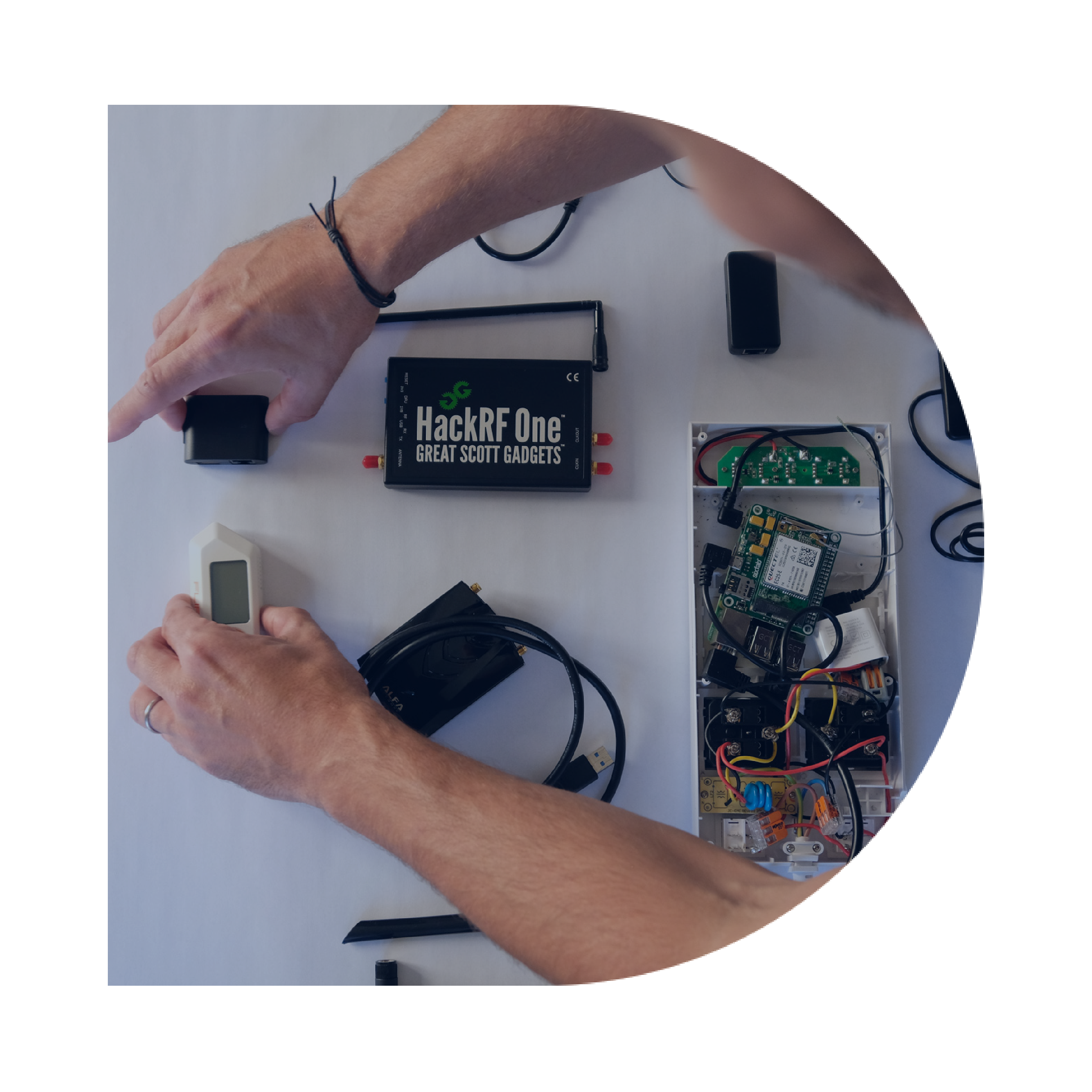
The R&D team closely monitors the latest technological advances and emerging threats.
Multidisciplinary, the team has experience in the offensive and defensive field, as well as a complete vision of your security challenges. It is illustrated through 3 missions:
MISSION 1
Search for vulnerabilities during complex audit missions using the reverse engineering method.

Discover the latest missions carried out by the team:
-
Heavy client audit of remote administration.
-
Comparative security study of EDR solutions as part of an RFP.
-
Study of hardware encryption solution
-
Development of a windows network sharing monitoring solution
-
Creation of custom hacking demonstrations
Looking for ZeroDay vulnerabilities
Every week, experts strive to find vulnerabilities from publishers. During the latest research, the RDI team discovered the following public vulnerabilities:
-

CVE-2019-1601: Elevation of privilege on vManage component related to Cypher code injection
-

CVE-2021-1480: Elevation of privilege on underlying vManage component system to execute commands as root – Cisco SD-WAN vManage
-

Vulnerability to Crack Xerox Printer Passwords – Cisco SD-WAN vManage
-

Injection of JavaScript code (XSS) in a black box allowing access to the backoffice – OCS Inventory
-

SQL injection in gray box, allowing to elevate its privileges on the application – OCS Inventory
-

Remote code execution on the underlying gray box system via SNMP functionality – OCS Inventory
-

Allows to read arbitrary files on the system via the exploitation of an SSRF – CMS Grav
Mission 3
Create and develop new tools for our consultants as well as for certain specific needs of our customers.
-
Crackstation
Collaborative password cracking tool:
- Use of multiple GPUs for increased computing power.
- Support hundreds of algorithms
- Use of specially designed dictionary list and optimize for XMCO needs
- Creation of custom rules
Voir plus
-
IAMBuster
Tool allowing automatic analyzes of Active Directory environment:
- User password audit
- Searches for compromise paths
- Identifying Vulnerable HPA Accounts
Voir plus
-
SMBRecon
Search tool for sensitive files within network shares:
- Regex support
- Multi-threaded for accelerated research
- Use of list of sensitive files consolidated by pentesters
Voir plus
-
ProtonPack
Post-operation tool in Windows environment:
- NTDS File Recovery
- Recovery of in-memory as well as local passwords
- Remote command execution
- Support for identity theft attacks (Pass-The-Hash, Pass-the Ticket, etc.)
Voir plus
-
Parpin
RedTeam tool to ensure persistence on compromised servers.
- Executing commands remotely
- Interactive Shell
- Proxy support
- Support for Windows and Linux environments
Voir plus